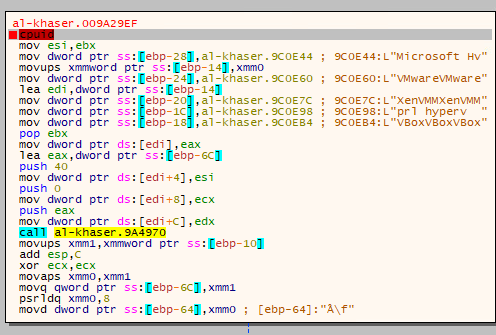
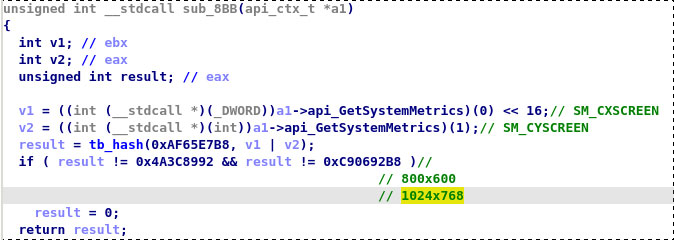
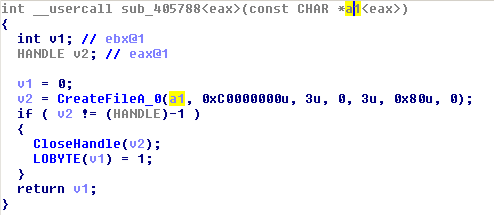
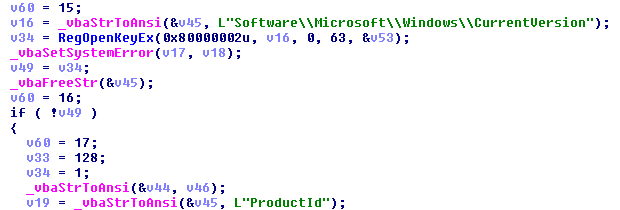
![Joe Security on X: "[Evasion] #VBA #Macro #Droppers include more and more Anti-VM and Anti-Sandbox tricks: ▷ WMI Win32_Process name and count checks ▷ AppGetNames name checks ▷ WMI Win32_Bios / ComputerSystem Joe Security on X: "[Evasion] #VBA #Macro #Droppers include more and more Anti-VM and Anti-Sandbox tricks: ▷ WMI Win32_Process name and count checks ▷ AppGetNames name checks ▷ WMI Win32_Bios / ComputerSystem](https://pbs.twimg.com/media/DsX3POaWkAEOESH.jpg)
Joe Security on X: "[Evasion] #VBA #Macro #Droppers include more and more Anti-VM and Anti-Sandbox tricks: ▷ WMI Win32_Process name and count checks ▷ AppGetNames name checks ▷ WMI Win32_Bios / ComputerSystem
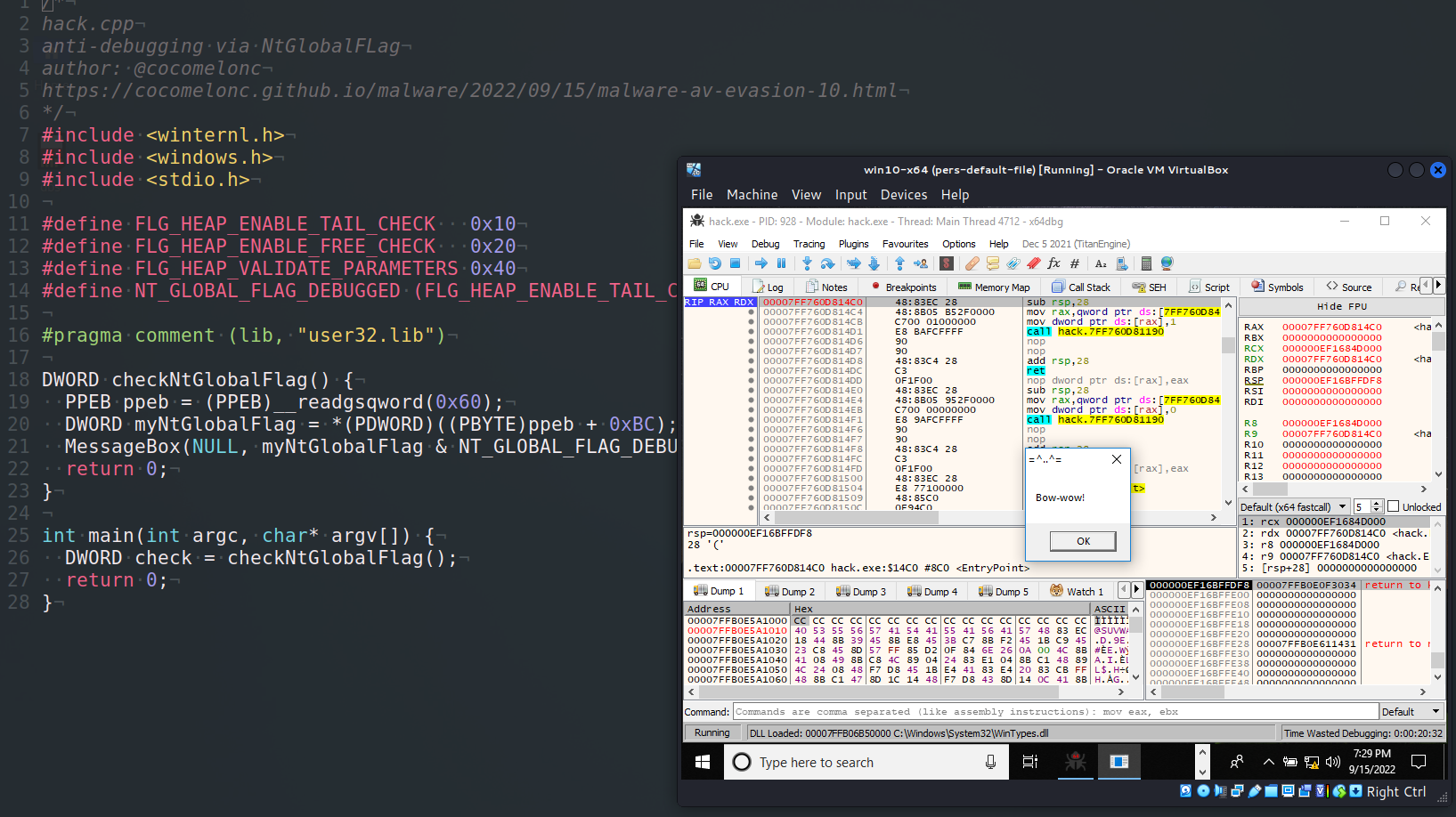
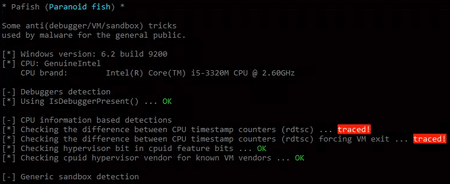
GitHub - secrary/makin: makin - reveal anti-debugging and anti-VM tricks [This project is not maintained anymore]